Cyberthreats in 2026 are not slowing down; they are evolving. Malware is becoming more sophisticated, harder to detect, and increasingly targeted. Whether you’re browsing on a laptop, managing finances on your phone, or working remotely, understanding today’s most common malware threats is essential to protecting your digital life.
In 2026, cybercriminals are leveraging automation, AI, and social engineering to exploit users in new ways. In this blog, we’ll dive deeper into learning about the most common types you can look out for and how UltraAV is made to protect you against them.
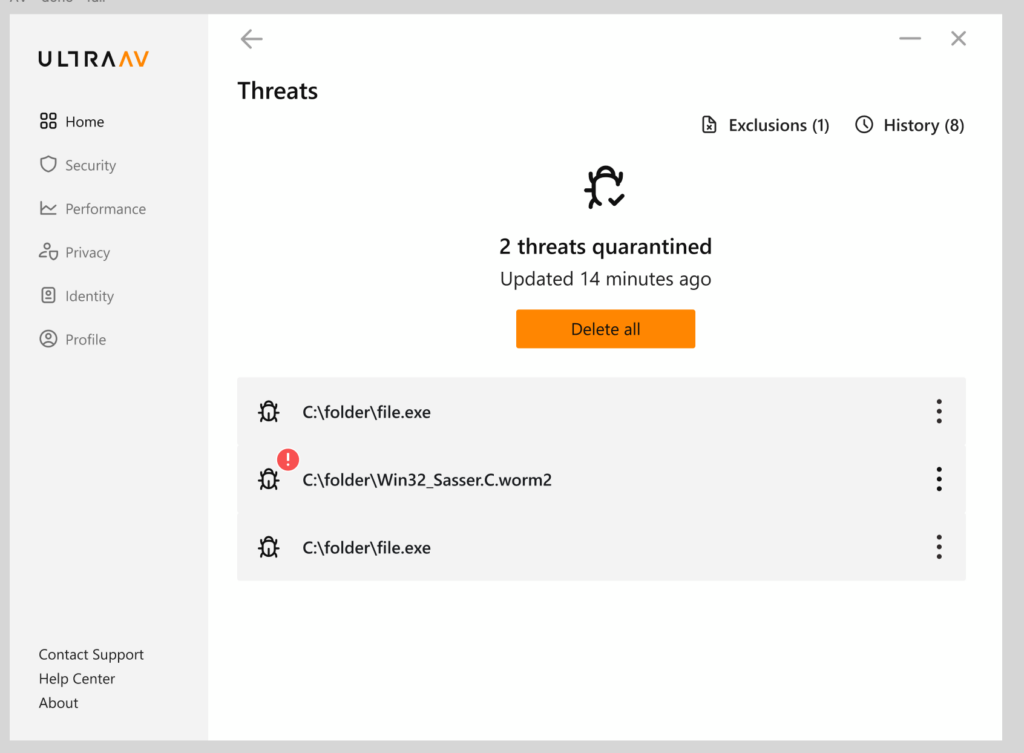
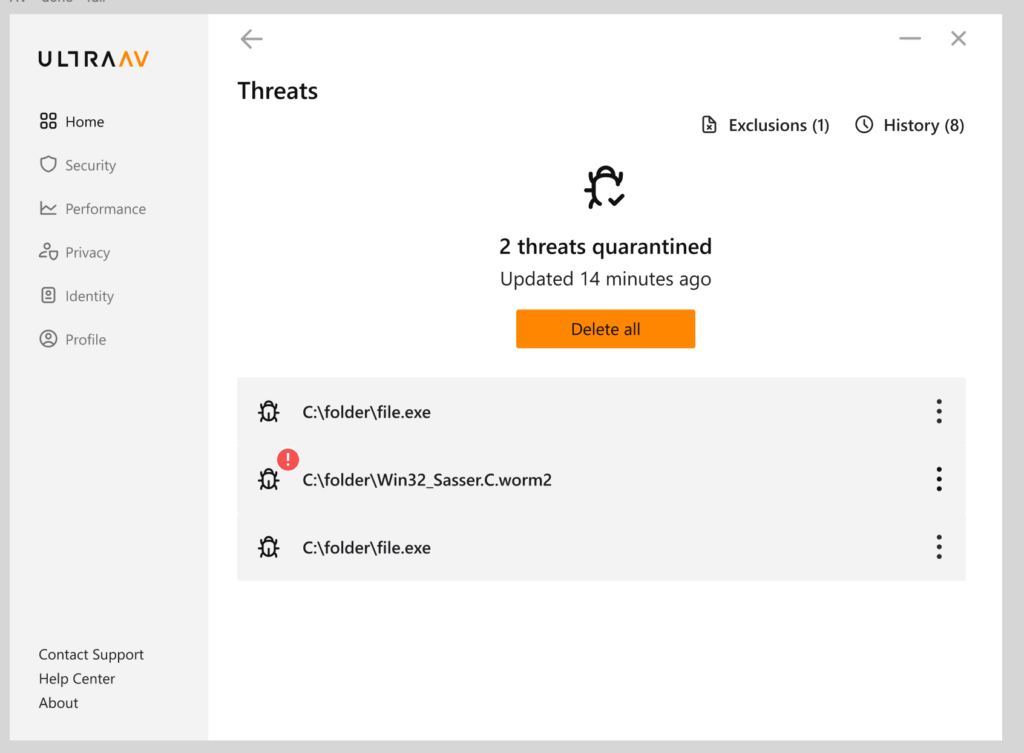
1. Ransomware
Ransomware remains one of the most damaging forms of malware. It locks or encrypts your files and demands payment, often in cryptocurrency, to restore access.
Why it’s still a major threat:
- Targets individuals and businesses alike
- Increasingly delivered through phishing emails and fake downloads
- Some variants now threaten to leak your data if you don’t pay
How to protect yourself:
- Avoid suspicious email attachments and links
- Regularly back up important files
- Use antivirus software with ransomware protection
2. Spyware
Spyware secretly monitors your activity, collecting sensitive information like passwords, browsing habits, and financial data.
Common signs:
- Slower device performance
- Unexpected pop-ups
- Unauthorized account activity
How it spreads:
- Bundled with free software
- Malicious apps or browser extensions
- Phishing links
3. Trojan Malware
Trojans disguise themselves as legitimate programs but contain hidden malicious code. Once installed, they can create backdoors for attackers to access your system.
Why Trojans are dangerous:
- Often appear trustworthy (fake apps, software updates)
- Can install additional malware
- Used for data theft and remote control
4. Adware
Adware bombards users with intrusive ads and redirects, often tracking your behavior to serve targeted content.
While not always destructive, it can:
- Slow down your device
- Lead to more dangerous malware infections
- Compromise your privacy
5. Phishing-Based Malware
Phishing is no longer just about fake emails. It’s now a primary delivery method for malware.
What it looks like in 2026:
- Realistic emails and messages
- Fake login pages that mimic trusted brands
- SMS (smishing) and voice phishing (vishing) attacks
Goal:
Trick you into downloading malware or revealing sensitive information.
6. Fileless Malware
Fileless malware operates in your system’s memory rather than installing files on your device, making it harder to detect with traditional methods.
Why it’s growing:
- Leaves little to no trace
- Uses legitimate system tools to execute attacks
- Common in targeted and enterprise-level attacks
7. Mobile Malware
With more people relying on smartphones for banking, shopping, and work, mobile malware is on the rise.
Common threats include:
- Malicious apps disguised as legitimate tools
- Banking trojans targeting financial apps
- Spyware embedded in downloads
8. AI-Powered Malware
AI-powered malware is a newer, rapidly scaling category that can adapt its behavior to evade detection and increase attack success rates.
What makes it dangerous:
- Learns from user behavior
- Evades traditional security systems
- Automates phishing and attack strategies
How to Stay Protected in 2026
Malware is becoming more advanced, but so are the tools designed to stop it. Staying protected requires a proactive approach:
- Keep your software and operating systems updated
- Avoid downloading apps or files from untrusted sources
- Use strong, unique passwords
- Be cautious with emails, links, and attachments
- Invest in comprehensive antivirus protection, like UltraAV.
Cyberthreats in 2026 are not slowing down; they are evolving. Malware is becoming more sophisticated, harder to detect, and increasingly targeted. Whether you’re browsing on a laptop, managing finances on your phone, or working remotely, understanding today’s most common malware threats is essential to protecting your digital life.
In 2026, cybercriminals are leveraging automation, AI, and social engineering to exploit users in new ways. In this blog, we’ll dive deeper into learning about the most common types you can look out for and how UltraAV is made to protect you against them.
1. Ransomware
Ransomware remains one of the most damaging forms of malware. It locks or encrypts your files and demands payment, often in cryptocurrency, to restore access.
Why it’s still a major threat:
- Targets individuals and businesses alike
- Increasingly delivered through phishing emails and fake downloads
- Some variants now threaten to leak your data if you don’t pay
How to protect yourself:
- Avoid suspicious email attachments and links
- Regularly back up important files
- Use antivirus software with ransomware protection
2. Spyware
Spyware secretly monitors your activity, collecting sensitive information like passwords, browsing habits, and financial data.
Common signs:
- Slower device performance
- Unexpected pop-ups
- Unauthorized account activity
How it spreads:
- Bundled with free software
- Malicious apps or browser extensions
- Phishing links
3. Trojan Malware
Trojans disguise themselves as legitimate programs but contain hidden malicious code. Once installed, they can create backdoors for attackers to access your system.
Why Trojans are dangerous:
- Often appear trustworthy (fake apps, software updates)
- Can install additional malware
- Used for data theft and remote control
4. Adware
Adware bombards users with intrusive ads and redirects, often tracking your behavior to serve targeted content.
While not always destructive, it can:
- Slow down your device
- Lead to more dangerous malware infections
- Compromise your privacy
5. Phishing-Based Malware
Phishing is no longer just about fake emails. It’s now a primary delivery method for malware.
What it looks like in 2026:
- Realistic emails and messages
- Fake login pages that mimic trusted brands
- SMS (smishing) and voice phishing (vishing) attacks
Goal:
Trick you into downloading malware or revealing sensitive information.
6. Fileless Malware
Fileless malware operates in your system’s memory rather than installing files on your device, making it harder to detect with traditional methods.
Why it’s growing:
- Leaves little to no trace
- Uses legitimate system tools to execute attacks
- Common in targeted and enterprise-level attacks
7. Mobile Malware
With more people relying on smartphones for banking, shopping, and work, mobile malware is on the rise.
Common threats include:
- Malicious apps disguised as legitimate tools
- Banking trojans targeting financial apps
- Spyware embedded in downloads
8. AI-Powered Malware
AI-powered malware is a newer, rapidly scaling category that can adapt its behavior to evade detection and increase attack success rates.
What makes it dangerous:
- Learns from user behavior
- Evades traditional security systems
- Automates phishing and attack strategies
How to Stay Protected in 2026
Malware is becoming more advanced, but so are the tools designed to stop it. Staying protected requires a proactive approach:
- Keep your software and operating systems updated
- Avoid downloading apps or files from untrusted sources
- Use strong, unique passwords
- Be cautious with emails, links, and attachments
- Invest in comprehensive antivirus protection, like UltraAV.
Protect Your Digital Life with Confidence
As malware threats continue to evolve, relying on basic protection is no longer enough. You need a solution that goes beyond detection, one that actively protects your devices, data, and identity.
If you’re looking to safeguard your device this year and stay ahead of emerging threats, a complete security solution like UltraAV can help keep your digital life secure, simple, and protected in one place.